Just because a site has a padlock doesn’t mean your data is safe.
Man-in-the-Middle attacks, also known as MITM attacks are one of the most deceptive forms of cybercrime today. They don’t require breaking your passwords or hacking into your device.
Instead, they quietly slip into the conversation between you and a trusted service, like your bank, email provider, or cloud platform without you ever realizing someone else is listening or altering the data.
Encryption is supposed to protect your data while it’s in transit. But MITM attackers exploit overlooked weaknesses in how devices connect and verify trust, allowing them to bypass encryption without ever cracking it.
In this article, you’ll learn how MITM attacks work, the methods used to bypass encryption, and the steps you can take to detect and prevent them before any damage is done.
What Is a Man-in-the-Middle Attack?
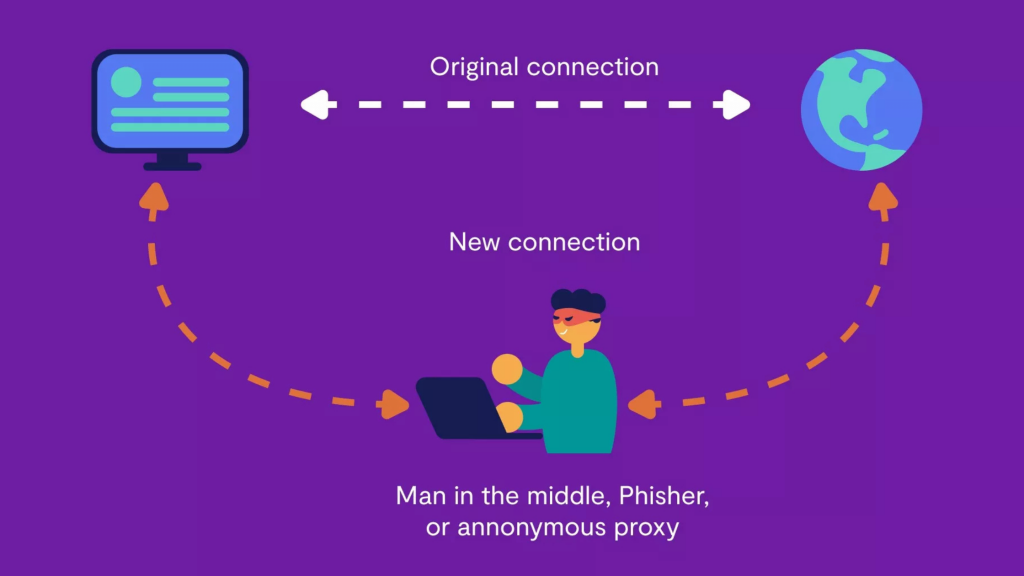
When two devices, such as your phone and your bank’s server, communicate online, they exchange data directly through a secure connection.
This is how you log in, send messages, or make payments. The system assumes that no one else is watching or altering the information in transit.
In a Man-in-the-Middle (MITM) cyberattack, a third party silently inserts itself between those two systems. They can intercept, read, and sometimes even change the data being passed back and forth. The original sender and receiver often have no idea someone else is involved.
Here are some common goals of MITM attacks:
Stealing Sensitive Data
Cybercriminals often use MITM attacks to grab login credentials, credit card numbers, or personal information while it’s in transit. Even if a website appears secure, an attacker in the middle can still intercept the data before it reaches its intended destination.
Hijacking Online Sessions
Once inside the communication stream, an attacker can hijack your session, essentially taking over your login without needing your password again. This allows them to act on your behalf without being detected.
Faking Identity
The attacker might send fake responses to impersonate the real service. For example, they could send you a login page that looks completely legitimate and capture your password when you enter it.
If you suspect someone is using your name or posing as you online, running a quick Name Lookup can help reveal where your identity may be appearing without your permission.
Spying or Altering messages
Not all MITM attacks aim to steal. Some are used to monitor conversations or change messages. This is especially concerning in business settings, where even minor changes can have significant consequences.
Who Is Most at Risk for Man-in-the-Middle Attacks?
These attacks can occur to anyone, but certain individuals and industries are more likely to be targeted. Knowing who’s at risk can help you stay safer online.
Financial Institutions
Banks, investment platforms, and fintech apps are prime targets because they handle high-value transactions and sensitive account data. Attackers often use MITM tactics to steal login credentials, intercept wire transfers, or manipulate account activity before it reaches the user.
Healthcare Systems
Hospitals and medical platforms store electronic health records (EHRs), insurance data, and prescription details, all of which are valuable on the dark web. MITM attacks here may involve fake login portals or intercepted data transfers between clinics, labs, or billing systems.
Industrial and IoT Networks
Factories, utilities, and other industries that use Internet of Things (IoT) devices are particularly vulnerable. Many connected sensors, control panels, and remote monitoring systems lack robust encryption or authentication, making them susceptible to interception and sabotage.
Small and Midsize Businesses (SMBs)
SMBs often lack the security resources of large enterprises. According to SCORE and the U.S. Small Business Administration, 43% of all cyberattacks target small businesses. MITM attacks on SMBs can result in significant data loss, reputational damage, and financial liability.
High-Risk Individuals
Certain people are more likely to be targeted, especially those who access sensitive data on unsecured networks:
- Executives and decision-makers
- Remote workers and freelancers
- Frequent travelers using public Wi-Fi
- IT administrators or developers with backend access
Even one stolen password or intercepted session can expose an entire system to compromise further.
How Cybercriminals Bypass Encryption in MITM Attacks
Encryption is designed to protect data while it’s in transit, but cybercriminals use clever tactics to get around it, without having to break it directly. Here are the most common methods that attackers use to infiltrate encrypted communication streams.
Rogue Wi-Fi Networks
Hackers often set up fake Wi-Fi hotspots with names like “Free_Public_WiFi” or “Airport_Guest” in public places like cafes, airports, or hotels. These appear to be regular networks, so people connect without hesitation.
Once connected, the attacker can view all data being sent and received. Even if the website uses HTTPS, the attacker might use SSL stripping. It’s a method that forces your browser to load an unsecured version of the site (HTTP), exposing your data in plain text.
This tactic is one of the many overlooked risks on public networks that cybercriminals routinely exploit to capture sensitive information.
ARP Spoofing and DNS Spoofing
In ARP spoofing, the attacker tricks your device into thinking their machine is the trusted destination. This lets them intercept your data before it reaches the real server.
In DNS spoofing, attackers tamper with the process by which your device finds websites. Instead of connecting to the actual address (like your bank), you’re silently redirected to a malicious site that appears identical but is controlled by the hacker.
SSL Stripping and Downgrade Attacks
Many websites automatically redirect users from HTTP to HTTPS. Attackers use SSL stripping to block that upgrade and keep your connection unencrypted, making it easy to steal login details or form data.
In downgrade attacks, hackers force your device and the server to communicate using outdated versions of SSL or TLS, older encryption protocols with known weaknesses. This gives them more opportunities to read or alter your data.
Compromised or Fake Certificates
Websites use digital certificates to prove their identity. If an attacker tricks your browser into accepting a fake certificate, it may show a secure lock icon, even though you’re not really connected to the trusted site.
This has happened before. In the Comodo and DigiNotar breaches, attackers issued fake certificates for major websites, letting them pose as trusted services without triggering browser warnings.
Evil Twin Attacks
This is a more advanced version of a rogue Wi-Fi attack. The attacker creates a network that appears exactly like a trusted one you’ve used before, with the same name and login page.
You connect, thinking it’s safe, and enter your credentials. However, the attacker can see everything you type and capture session cookies, passwords, or even redirect you to phishing sites without your knowledge.
How to Protect Yourself From MITM Attacks

Although Man-in-the-Middle attacks are sneaky, there are simple steps individuals and businesses can take to reduce the risk. Here’s how to stay protected.
For Everyday Users
- Avoid public Wi-Fi for sensitive transactions: Cafes, airports, and hotels are common targets. Don’t log in to banking or private accounts unless you’re on a secure, trusted connection.
- Always check for HTTPS and the padlock: Only enter personal info on sites that start with “https://” and show a padlock. If it’s missing, don’t continue.
- Use a reputable VPN: A VPN adds a layer of encryption, even on public networks, making it harder for attackers to spy on your activity.
- Keep your devices and apps updated: Security updates fix known flaws. Stay protected by regularly updating your phone, browser, and other software.
- Use reverse lookup: If you think your information has been exposed, even if you’re not sure where, a quick Reverse Lookup can help you connect the dots and find out what’s out there before it’s too late.
For Businesses and IT Teams
- Use HSTS to force secure connections: HSTS tells browsers to always use HTTPS, blocking SSL stripping and improving website security.
- Enable DNSSEC and encrypted DNS: Protocols like DNSSEC, DoH, and DoT protect DNS lookups from being hijacked or redirected.
- Train employees on network threats: Educate staff to recognize fake Wi-Fi networks, phishing pages, and browser warnings to prevent attacks early.
- Scan for rogue access points and ARP spoofing: Use monitoring tools to catch fake networks or spoofing attempts before they cause harm.
Final Word
What many people don’t realize is that a Man-in-the-Middle attack is often just the beginning of a larger scheme.
Once an attacker captures your login details or personal information, they can launch further cyberattacks, open fake accounts, reroute your emails, or impersonate you across multiple platforms.
If you doubt that your identity has been compromised or you’ve noticed unusual activity tied to your name or accounts, it’s worth speaking with a Search Specialist at Social Catfish. We can help trace digital footprints, identify misuse, and guide you on the next steps to take.
Here’s what one of our users has to say:
“ERIN was really helpful with everything I asked and I was set aside with the accuracy and letting me know what steps I need to take next very helpful.” – Barbara Spalding


 Multiple Faces Detected
Multiple Faces Detected





















