The internet and everything that comes with the Information Age has ushered the world into an era of massive globalization and a vastly wider scale of connectivity, and although these both bring a lot of positive changes to the way we go about our daily lives, they have also opened the door to a lot of insidious crimes.
These cybercrimes, such as hacking and phishing, aren’t actually unique to the digital world– such scams are simply virtual versions of real-world cons, which are broadly referred to as “social engineering attacks”.
What is social engineering?
Although the term “social engineering” sounds harmless or even quite positive at first, in the context of security, it’s a term that actually refers to the art of manipulating people into providing you with their sensitive personal information. This differs from the social engineering done in the context of social sciences and organizations, where groups of people are “influenced” to change behavioral patterns instead of manipulated with malicious intent.
The security-related “social engineering” are those linked to the rising attacks, which can occur both online and offline.
Types of Social Engineering Attacks
Phishing
Phishing schemes are social engineering attacks that are designed to imitate a source you trust. This source could be a close friend or a known organization (like a bank or a charity). Following this imitation is a request crafted in such a believable way that you will be prompted to do something you wouldn’t do in any normal circumstance, like send cash to an address, or hand over your sensitive personal information.
Some of the most common phishing schemes happen on emails, where social hackers email you while posing as your bank or as a lottery event. These kinds of emails usually ask for your bank or credit card information as a part of a long questionnaire, still under the guise of the organization you trust. These kinds of emails tend to go the extra mile, using logos and graphics that are associated with these organizations.
Phishing scams are not only limited to the digital world, as they can happen via snail mail as well.
Trap Phishing
Another type of phishing scheme is something known as Trap Phishing. Trap phishing is where the target is linked to a fake website imitating a website that’s familiar to the target. These sites are usually copies of social media sites or retail stores like Amazon. The link directs the target of this scam to a page resembling a login page. Realizing they are logged out, they “log in” using their credentials and are redirected to the real website. This gives the hackers both the username and password of the target, giving them access to the real account found on the real website.
Other phishing schemes occur when a hacker gets ahold of an email account belonging to your friend or loved one. Since the account has access to all of your friend’s contacts, the hacker can then send them messages posing as your friend, slyly crafting statements to manipulate their friend pool into doing what they want them to do.
Baiting
Now that you know what phishing is, the next question is: what is baiting?
Baiting schemes are exactly what the name implies: social hackers lure you with some sort of bait– it could be a free movie download, free airline tickets, or a way to see who’s invisible on your chat list– and once you take the bait, you either end up downloading some malware or end up in a trap phishing site. Either way, you will be losing some valuable information, and might even get locked out of your accounts or your computer or device.
Creating Conflict and Dissonance
Sometimes, social hackers can be more psychologically malicious with their methods. Some of these hackers would rather hack people than systems, and so they photoshop screenshots of chat/message logs or posts on social media, usually adding in something extremely controversial or disagreeable, to spark real drama and arguments. Sometimes, this kind of tampered with and untrue information or information is taken out of context is also used in even more elaborate crimes, like bribery or extortion.
How to Avoid Social Engineering Attacks
Now that we’ve gone through the most common types of social engineering attacks, it’s time to run through the best ways to avoid them.
First, be wary of emails that call you a “winner” of a certain prize you did not know you opted for, and any email or printed form that asks any information from you, and if your friend asks something unusual of you, make sure to verify it’s them by meeting them first in person or by talking to them via call.
Be wary of any offer that seems too good to be true from an unfamiliar website. Just like in real life, unfamiliar places and people should not be trusted with your information. When encountering these offers, stop and think for a while. Do some research. Check out third-party reviews of the website you are on or the organization you are dealing with. Call a few official numbers. Any website that lets you download a file or fill out a form should take a few more moments of consideration before diving into them.
Carefully check out if the website’s URL matches the one you’re familiar with– better yet, it’s best to take control of your URLs and type them yourself. Make sure to check if the sender of company emails or organizational emails is from senders you’ve already added to your contacts.
With these few considerations in check, you will manage to keep yourself safe online and offline.
Conclusion
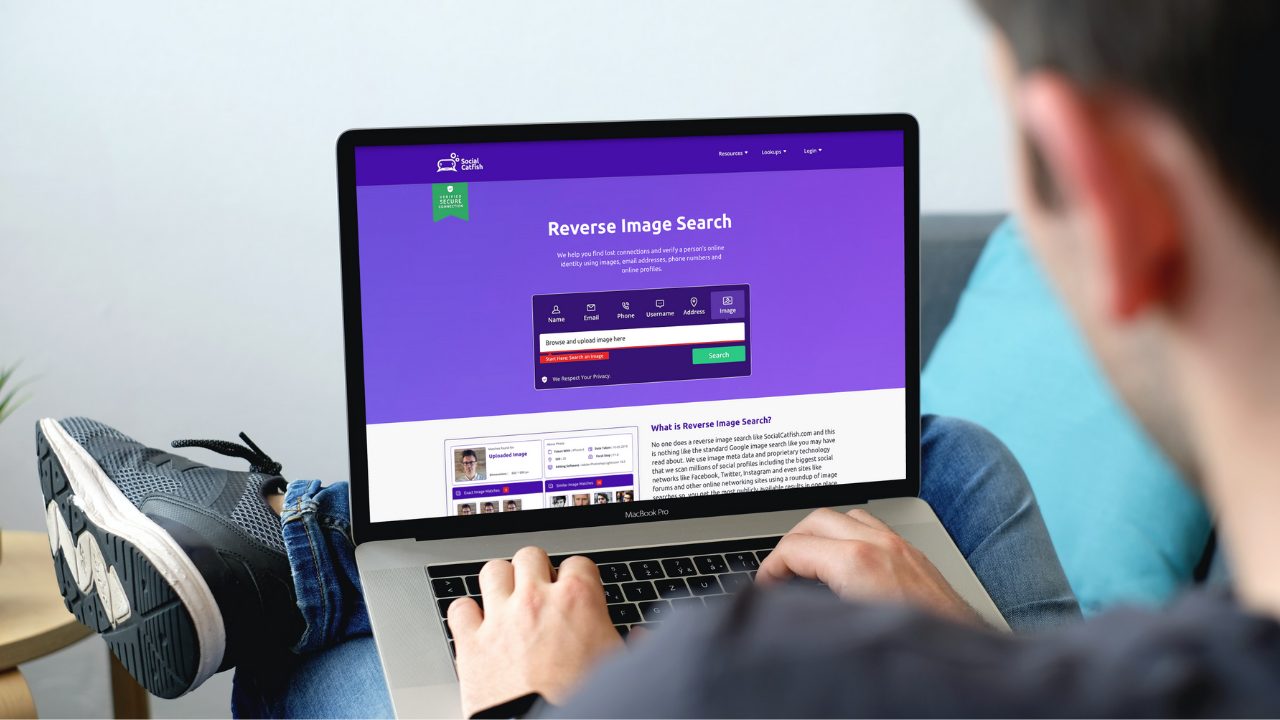
Doing business online has always come with risks. Over the last couple of years, as much of our lives have moved to the internet, the risk has become invisible to many of us. socialcatfish.com empowers you by giving you the tools to have complete visibility. If you are suspicious that someone might be a scammer, use the search bar below to find out the truth. A reverse search bar below will give you a 360 view of someone’s digital footprint to let you know if they can be trusted. Use the search bar below to run your first search today.


 Multiple Faces Detected
Multiple Faces Detected